Detect, Prevent and Remediate Ransomware
Submitted by Sophos Channel on
Signatureless Threat and Exploit Detection with Root Cause Analysis and Roll Back Capabilities are Critical Next-Gen Technologies
The number of attacks companies of all sizes face every day is almost incomprehensible. This includes a near daily dose of ransomware, zero-day exploits and other malicious malware carried out through increasingly clever phishing scams. But, this isn’t anything new. We’ve seen these cybercrime trends building year after year. What is new, and perhaps even more concerning, is that traditional malware has morphed into two major attack vectors that are more difficult to detect and thwart with conventional endpoint security solutions.
To further complicate matters, cybercriminals can use these two attack vectors together to strengthen their effectiveness and target weak spots. The first vector is “user-focused” malware that leverages social engineering to trick users into opening emails and accidentally clicking on malicious attachments and URLS from sources who appear trustworthy. Without realizing what they’ve done, users have potentially opened up their company to cyberattacks.
The second attack vector I want to highlight is the “vulnerability exploit.” Cybercriminals proactively look for weaknesses in software that will let them send threats into a company’s network. Patching and updating software on a regular basis is a known “best security practice,” but unfortunately, businesses still struggle to keep up with patching routines that help protect against these vulnerabilities. Our research shows that 90 percent of data breaches are the result of exploit kits, and frustratingly, 90 percent of those exploit kits are built from known vulnerabilities. Inevitably, companies will get hit, yet more than 60 percent of enterprise IT staff lack incident response skills. Meaning, when businesses do get attacked, they struggle to mitigate any damage and loss of sensitive data.
That’s why we recently released Sophos Intercept X to enable our channel partners, MSPs and customers to more quickly identify zero-day malware, unknown exploit variants and all types of ransomware, and take immediate steps to detect, prevent and remediate the damage.
Sophos Intercept X incorporates four critical technologies:
- Signatureless Threat and Exploit Detection: Anti-malware and anti-hacker defense that block zero-day, unknown and memory resident attacks and threat variants without the need for file scanning
- CryptoGuard: Anti-ransomware innovation that identifies rapid encryption activity within a few files to block ransomware before it can lock and cripple systems. Rolls back encrypted files back to their pre-attack state with no loss of data.
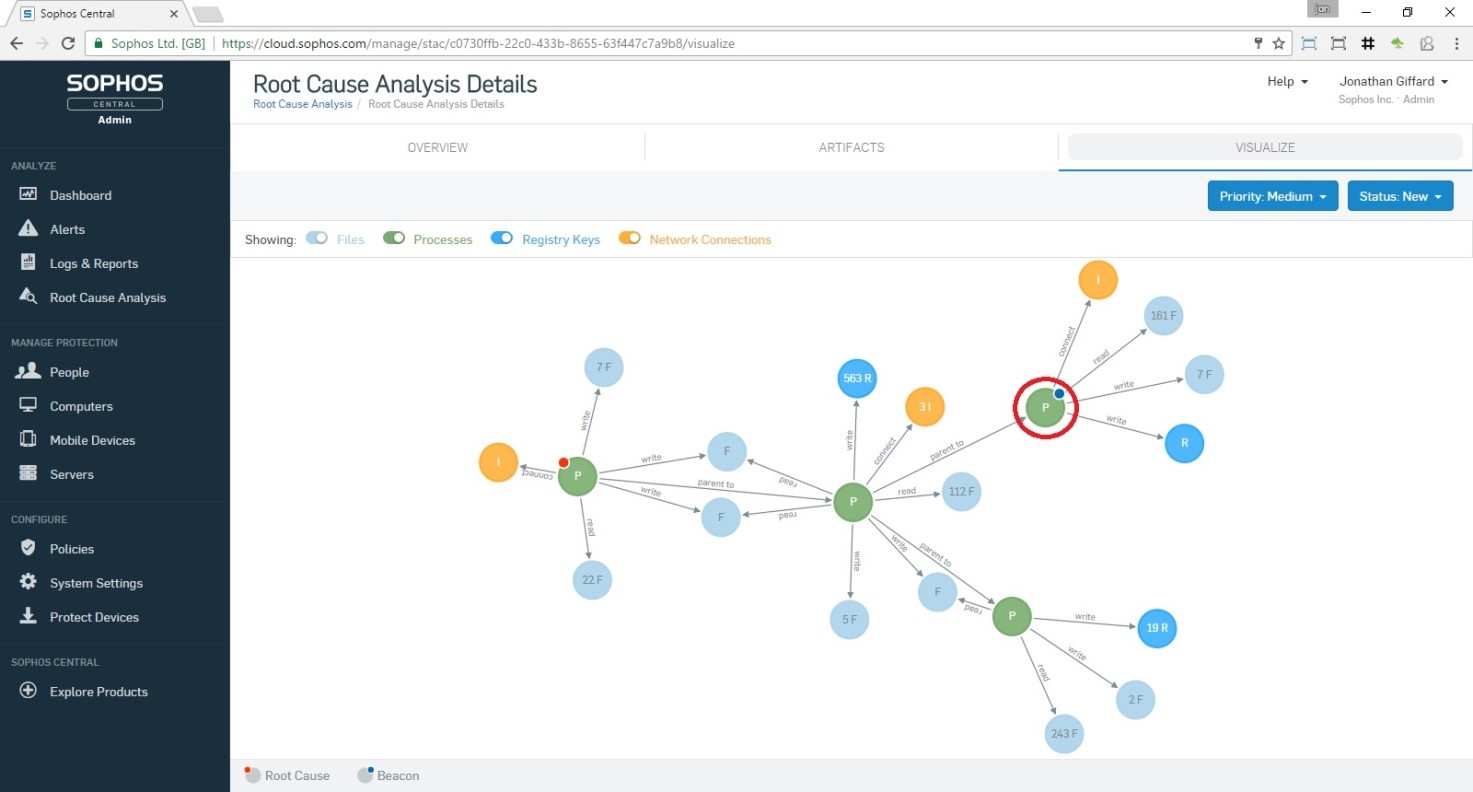
- Root Cause Analysis: A simple visual and interactive guide of an attack event that shows where the attack came in, what it affected, where it stopped and provides recommendations to prevent a similar attack in the future. Below is an example of these details mapped out.
- Sophos Clean: Hunts for and removes any trace of spyware and deeply embedded, lingering malware.
Detecting and preventing threats is always the first step. The next critical step is to leverage information on the root cause of an attack to make the remediation process simple and quick. This includes providing incident response capabilities for both single endpoint computers and across an entire enterprise. Attackers are adept at intelligence-gathering, and you should be too. Intelligence is a new critical component of remediation and prevention. Root cause analysis reveals the “who, what, where, when and how” of a cyberattack or data breach. Sounds complicated, but in fact, with Sophos Intercept X, it’s just the opposite.
One other important piece of Sophos Intercept X is its ability to run alongside existing endpoint security software from any vendor, immediately boosting protection levels that detect and stop ransomware and other malicious code before executing. For Partner and MSPs looking to build their next-gen business, especially at a time when ransomware is rampant and at the top of every customer’s worry list, this capability is invaluable. With Intercept X, partners and MSPs can immediately add anti-ransomware and anti-exploit solutions to their portfolio.
We’d like to hear from you. Please review our Partner Program and Sophos MSP Connect to learn more about stopping ransomware today.
Scott Barlow is vice president, Global MSP, at Sophos, a leader in network and endpoint security products, services and technologies. He oversees all MSP strategy, business direction and sales worldwide, with an emphasis on building revenue, marketing programs and relationships with partners.